
Primarily, cryptos work using Blockchain technology, which is a complex mechanism to understand. That cryptography is used as a prerequisite to secure information goes without saying.
As you have read previously, privacy, decentralization, and security are among the many things that make cryptocurrencies popular.
They work on a peer-to-peer basis, unlike ordinary currencies that require the authority of a central bank.
The entire structure of crypto is based on several techniques and methods, working together to keep the network running smoothly.
Crypto custody refers to the management and safeguarding of digital assets.
Now, what are those methods and techniques?
Cryptography
Cryptography is a security mechanism used to ensure that certain information reaches the right person. It helps avoid any unauthorized access.
It uses mathematical concepts and algorithms to keep messages and information secure and sound. Not only in Cryptocurrency but in daily life also, cryptography helps secure our web browsing experiences, online payments, among other things.
Since our area of focus is Cryptocurrency, we will learn about cryptography in the same context.
Cryptography in Cryptocurrency

As you know, Cryptocurrency is a highly secure and encrypted form of virtual currency used for online transactions.
It is worth noting that there are several cryptography techniques that shield any information shared or exchanged through Cryptocurrencies.
Let us discuss some of the cryptography methods used to encrypt data in the context of Cryptocurrencies.
Symmetric Encryption Cryptography
This method uses a Secret Key (aka Private Key), which we can define as a method to encrypt and decrypt messages in a conversation.
Under Symmetric Encryption Cryptography, the secret key is the same for encryption, transmission, and decryption of a message. It is easy and less complex yet provides a good level of security to a particular communication.

Consider an example where letters are encrypted as numbers in a text. When a text ABCD is sent, it is encrypted as 02040608. Similarly, TEXT will be encrypted as 22072622.
When the recipient receives the message, they have to use the same methodology to decrypt it, after which the algorithm will reverse its action to make sure the message is back in a readable form.
Even if someone else gets access to the text, it would be of no use without a key.
Asymmetric Encryption Cryptography
Unlike the previous method, it uses two unique keys, private and public, to encrypt, transmit, and decrypt data. Anyone can access the public key, but only the receiver can access the private key.
The text can be encrypted using the receiver’s public key but only be decrypted using the receiver’s private key.
Consider a daily life example where any of your social media friends can send you a text, but no one else can access them because only you know the password to your account. Here, your password is your private key, while your social media id or handle is the public key.
When Satoshi Nakamoto created Bitcoin, he used an asymmetric encryption known as Elliptical Curve Cryptography.
Hashing
The cryptographic integrity of blockchain in Cryptocurrency is maintained through Hashing. It helps in verifying data on the network.
Any data, regardless of its type and size, can be converted into a unique string of text using Hashing. After conversion, the hash produced by the data is always the same length.
It is used to write new transactions, add timestamps to them, and reference them in the previous block.
Block mining is only made possible by the successful usage of the hashing function. Moreover, it isn’t easy to reverse a hashing function.
The Blockchain Technology

It would not be wrong to say that blockchain is the backbone of Cryptocurrency. It plays a dominant role in the latter’s existence. But what is blockchain?
In simple terms, it is a way of collecting and storing information that is almost impossible to alter by unfair means.
Blockchain is a digital ledger containing records of transactions in blocks, duplicated and spread across the entire network of computer systems on the blockchain.
One must note that the data is first stored in a block, and when its storage capacity is fully utilized, it is chained into the previously filled block, thereby forming a blockchain.
Every block in the chain has several transactions, and with every new transaction on the blockchain, the ledgers of all the participants are updated.
Blocks are securely linked to each other using cryptography, and, as mentioned previously, every block contains a hash pointer as a link to the previous block along with transaction data and a timestamp.
Though blockchain technology can be used to store different types of information, it has been popularly used only as a ledger.
Since Cryptocurrency is a decentralized form of currency, blockchain technology is used under it in a decentralized way making the data entered in a block irreversible and permanently viewable to every participant.
It is collectively managed by a peer-to-peer network to make it work as a distributive ledger. We will understand how a cryptocurrency transaction takes place in another blog, which would give you an almost practical experience of trading in cryptocurrencies.
What makes Blockchain secure?
Several features make blockchain predominantly secure and safe. To start with, new blocks are always added to the end of the blockchain in a linear and chronological manner, making any tinkering with the data impossible.

To alter the data, one has to gain a majority consensus. Why? Because every block contains, along with its own hash, the hash of the previous block and timestamp.
Now that you know a hash is a cryptographic technique, you also need to understand that it is created based on mathematical functions that can turn digital information into a string of numbers and letters.
If someone tries to alter that information, the hash code would also change, alarming everyone on the network.
First Usage of the Blockchain Technology
Though David Chaum had discussed a decentralized approach to currency usage, it was not until Stuart Haber, and W. Scott Stornetta outlined it in their paper in 1991 that a collective discussion regarding the technology began among domain experts.
Their research aimed to create a system that would make tampering with timestamps impossible. They proposed calculating hash values of documents before saving them with a timestamp.

Next, they said, was to link up the records in a data structure with the help of hashes of previous records’ certificates.
Though the ideas were mooted in 1991, their application in the real world could only see the light of the day in 2009, when Bitcoin was released.
Satoshi Nakamoto, the pseudonym behind Bitcoin, has mentioned Stuart and Scott multiple times, recognizing the efficacy of their research.
Nodes
The basic unit of a data structure is called a node. Nodes can be linked to each other in the form of a tree data structure or a linked list.
In the context of Cryptocurrency, a computer connecting to a cryptocurrency network while sharing information and following rules is known as a node.
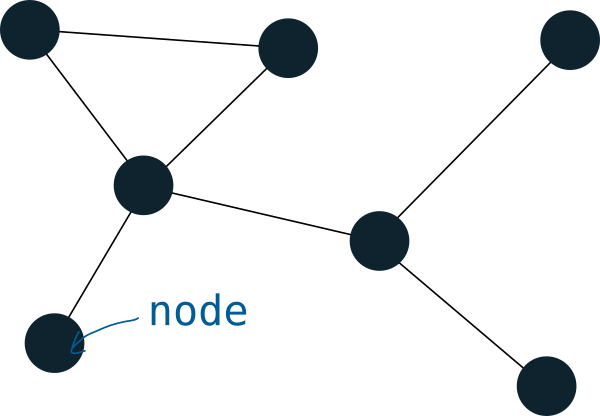
Its main objective is to support the network via validation and relaying transactions. Simultaneously, it also has to get a copy of the entire blockchain.
There can be two types of Nodes in a crypto network: Full Nodes and Lite Nodes. Full Nodes are the ones that fully validate blocks and transactions.
Most of the full nodes also accept transactions from other full nodes and blocks, validate them and relay them to further full nodes. If we talk of Bitcoin, full nodes fully enforce all the rules of Bitcoin.
On the other hand, Lite Nodes need the help of full nodes for functioning. They do not store the entire blockchain and are only tasked with verifying transactions using Simplified Payment and Verification (SPV).
How a Node Relays a Transaction?
Each node contains a copy of the blockchain of the Cryptocurrency supported by it. During the event of a transaction, the particular node creating the transaction broadcasts its details to other nodes using encryption throughout the node network to make the transaction known.
Mining
To understand the concept of Mining in terms of Cryptocurrency, we have to take the example of Bitcoin to make things simpler.
On the blockchain network, the process of circulating new Bitcoins is known as Mining. Moreover, it is also a critical aspect in maintaining and developing the blockchain ledger.
Who mines Bitcoins?
Common people! Yes, anyone from the general public can be a bitcoin miner provided they have a Graphics Processing Unit (GPU) or an Application Specific Integrated Circuit (ASIC) necessary to set up a mining rig.
Miners are paid in Bitcoins for their continuous efforts in helping run the network. Not only do miners infuse new bitcoins, but they also verify the transactions being added to the blockchain ledger.
I will discuss more about Bitcoin Mining in upcoming blogs.
Wallets
A wallet is nothing short of a prerequisite before someone starts using or trading in a cryptocurrency. To understand the concept in simple terms, take the example of payment applications.
Most of them have an in-built wallet where you keep the money and make payments to whomever you want.

A crypto wallet also does the same thing but with a whole lot of security features. It stores the public and private keys, which we have discussed earlier, for a particular individual to facilitate the exchange of Cryptocurrency.
While the public key acts as an address and allows others to send crypto, the private key allows individuals to spend the Cryptocurrency and write in the public ledger.
One wallet can hold multiple cryptocurrencies. There can be several wallets, including desktop wallets, hardware wallets, mobile wallets, web wallets, etc.
There are many other factors responsible for the working of cryptocurrencies but knowing each one of them is not necessary. They are too technical from a beginner’s and an investor’s point of view.
What you have to keep in mind is the fact that if cryptography is the base of cryptocurrencies, blockchain technology is its backbone.
Nodes, Mining, and wallets are essential factors in making the decentralized and ambitious cryptocurrency work.
If you liked reading the blog, please subscribe to The Word Street Journal and promote quality content.



